Can You Upload Copyrighted Stuff on Virustotal
VB2017 paper: VirusTotal tips, tricks and myths
Randy Abrams
Contained security analyst, The states
Copyright © 2017 Virus Message
Abstract
Outside of the anti-malware manufacture, users of VirusTotal generally believe it is but a virus-scanning service. Most users quickly reach erroneous conclusions about the significant of various scanning results. At the same fourth dimension, many very technical people are unaware that VirusTotal provides a wealth of contextual and forensic information. Most people do not realize that VirusTotal is a multi-directional threat intelligence feed as well.
Afterward a brief introduction to the history of VirusTotal and its part in today's security ecosystem, the myths listed below will exist debunked, and little-known features of VirusTotal will be demonstrated.
- Myth ane: VirusTotal can exist used to perform comparative testing.
- Myth 2: Detection of malware on VirusTotal means the scanner has detection of the malware.
- Myth three: Lack of detection on VirusTotal means the file is safe.
- Myth four: Lack of detection on VirusTotal means the scanner doesn't find information technology.
- Myth five: Faux positive ways imitation positive.
- Myth 6: More than is better.
- Myth 7: Malicious website means malicious website.
Information that can be obtained using the tabs for 'File Details', 'Relationships', 'Additional Information', 'Comments', and 'Votes' will be reviewed. Some additional resources bachelor to users will be touched on, and the need to read the terms of service will be emphasized.
Disclaimer: The most pedantic readers of this paper will at times take issue with me saying 'anti-virus' instead of 'anti‑malware', and 'virus scanner' instead of 'malware scanner'. With the exception of the discussion of specific types of malware, the terms 'virus' and 'malware' are synonymous for virtually people. The battle for differentiation was lost more than a billion malware samples ago. Symantec (Norton), McAfee, Trend Micro, ESET, Kaspersky, Bitdefender, and many others include the word 'Antivirus' in the names of their products.
REM That's enough to testify my indicate. (A reference to the Concept macro virus which displayed a dialog box containing the text 'i'. Inside the macro was a remarked line reading 'That'southward enough to prove my point'.)
VirusTotal was launched in June 2004 by the Spanish security visitor Hispasec. In June 2012 VirusTotal was acquired past Google. Today, VirusTotal is a wholly endemic subsidiary of Google. Initially, VirusTotal began as a web-based virus‑scanning service utilizing a handful of virus scanners. VirusTotal has since grown to include dozens of scanners, threat analysis and other contextual threat intelligence.
VirusTotal is widely known as a virus‑scanning service and information technology is true that VirusTotal will run a file through a battery of anti‑malware products. However, many people – including IT professionals – do not know that VirusTotal accepts input such equally IP addresses and domains, or that much more information is available besides the results of a scan.
Getting samples to VirusTotal
In that location are multiple ways to submit files, URLs, etc. for scanning. The method that most people are familiar with is using the landing folio at world wide web.virustotal.com. Files, file hashes, URLs, domain names and IP addresses can all exist submitted.
- If there is no particular urgency, files can be sent via email. Email submissions take the everyman priority for scanning of all of the other methods [one].
- VTZilla is a Firefox extension that facilitates the scanning of files and URLs via the correct-click context carte on links and the download dialog box. Links in emails tin can also be submitted to VirusTotal for phishing [two].
- The VirusTotal Windows uploader adds a context card detail to Windows Explorer. Files can as well be dragged and dropped onto a desktop icon and there is command-line functionality [iii].
- VirusTotal has an Android application that volition provide scan results of apps on the device. As VirusTotal notes, the VirusTotal app does not provide protection, it is only for reporting. VirusTotal will not forbid a threat from getting onto the system, and information technology will non remove malicious apps [4].
- At that place are public and private APIs. The public API is free and provides more information than the average user even knows is present on VirusTotal. To get started it is a requirement that you sign up to the VirusTotal community. VirusTotal does not spam people and the community shares a lot of information.
Upon signing upward y'all will obtain a free key that is required to employ the API. The documentation for the API includes code samples and can be establish at [v]. The frequency of submissions immune using the public API is express, only is probably more than adequate for most users, as is the richness of data returned.
The private API is well known to security companies and to most It professional that utilize threat feeds. The private API allows for a college rate of submissions, but also adds the ability to retrieve significantly more information from VirusTotal. More information about the individual API can be found at [vi] and [vii].
Submitting files, etc. is the piece of cake office. It is when the results are returned that VirusTotal mythology kicks in. VirusTotal is Zeus and each virus scanner is a lesser deity. The lesser deities often appear to disagree with each other, fifty-fifty when they practice concur on something.
I am confused already
The genesis of a myth oft lies in the oral tradition of an incorrect, or partially right caption of something that is misunderstood to begin with. At some betoken the myth is transcribed and so that it can exist cited as fact – as some may claim is the example with this newspaper. For the average user who simply wants to know if a file is safe, results such every bit PUP, PUA, potentially dangerous awarding, etc. tin can be quite confusing. In some cases detection reports will indicate PUPs, PUAs, riskware, trojans, and more for the same sample. These classifications may lead to confusion as to whether or non their scanner is protecting them.
Consider this riddle: If he is she, and so who is he, and is a canis familiaris a fish? The reply will exist provided in due grade.
The Rabbit of Caerbannog – 'Well, that's no ordinary rabbit!'*
*(A reference to Monty Python and the Holy Grail.)
Many years ago, an e-mail containing a file claiming to exist about a cute or funny bunny rabbit was circulated. The bailiwick line and bulletin body indicated the fastened item would display a bunny rabbit and take audio that must be listened to. Upon engaging in the deadly 'double-click of expiry', a dialog box saying 'GOTCHA. HAVE A Prissy DAY' would be displayed and a vocalization from the computer would yell 'Hey everybody I'm watching porno over here, woo hoo!'
 Figure 1: Not a bunny rabbit.
Figure 1: Not a bunny rabbit.
Peradventure you call up the NiceDay macro virus. This is not the NiceDay macro virus.
Let's run rabbit.exe through VirusTotal and see what the results are.
The results include vii detections of Gen:Variant.Zusy.Elzob.14268 and two other miscellaneous versions of Zusy (Figure 2). A search for Zusy.Elzob.14268 returns many Zusy Elzobs, but none are the 14268 variant. Most of the descriptions of Zusy Elzobs betoken that these are trojan downloaders, password stealers, and other not so nice applications. The results returned from VirusTotal include indications of potential bots, downloaders, and other quite nasty types of malware. Nine out of 36 indications are for a Zusy of some sort. Six of 36 bespeak a generic trojan of some sort. At that place are indications of unclassified malware, riskware, a PUP, and Artemis!E88B23DD3445. Of note, 12 of the results include the word 'Joke' in the clarification. Finally, 20 of 36 scanners display no detection. So, who is right?

Figure 2: Results of running rabbit.exe through VirusTotal.
The answer lies in the riddle 'If he is she, so who is he, and is a dog a fish?'
The English word 'she' is pronounced 'he' in Hebrew. The English give-and-take 'he' is pronounced 'who' in Hebrew. Finally, the English word 'dog' (pronounced daag) is the Hebrew word for fish.
The scanners are speaking different languages, some maxim the aforementioned thing and some proverb different things, and and so the meaning of the scan results is quite confusing. If he is she and who is he, then we are probably speaking Hebrew and indeed a dog is a fish. Only if we are not speaking Hebrew, then a dog is probably not a fish. Permit's try a couple of sentences that may or may not accept Hebrew words interspersed with English words.
I was out walking my canis familiaris in the snowfall when I ran into a friend of mine. He was wearing a bikini. I always knew he was strange.
Did I say I was walking a fish in the snow and I saw a guy wearing a bikini, or did I say I was walking a fellow member of the canine family in the snow and I saw a daughter wearing a bikini?
You tin can't tell from the results of the scan of rabbit.exe whether you are looking at a program that is a joke, or if the program is malicious. The Rabbit application simply made racket and displayed a bulletin box. It would exist understandable if one were to assume this application was intended to induce laughter, and perhaps cause a footling embarrassment.
Choosing non to observe rabbit.exe is a valid strategy. Choosing to observe rabbit.exe is also valid unless the detection actually is a false positive. Because of the ambiguity and subjectivity of the designation of trojan, PUP, PUA, PDA, etc., it is perfectly valid to notice rabbit.exe.
Consider the following real-world scenario:
An employee in a call eye opened the rabbit.exe attachment. The sound of someone in a cubicle yelling 'Hey everybody I'grand watching porno over here, woo hoo!' was heard across the floor. Indeed it was riskware, and/or a PUP, and/or a PUA, and/or a trojan, and/or an inappropriate joke in that situation. I would guess that the employee who sent the email realized the risk when he was fired. Depending on the visitor, the customers who heard it may have thought 'that explains the lack of customer service'. Choosing non to detect the file can be justified as well. When I commencement encountered the file I laughed – I withal do. To me, it was a joke.
Considering neither detection nor non-detection is wrong, the file is not valid every bit a office of a comparative exam. Information technology is possible that a production did generate a false positive, but since the file cannot exist used in a comparative test information technology is irrelevant. A competent tester volition remove the file from the test gear up… and and then send it to a friend.
It is easy to empathise why the user may call up they have the rabbit virus and that the scanners that did not detect it are non as good as the scanners that detected it. And so a myth is built-in.
Myth 1: VirusTotal can be used to perform comparative testing
Rabbits are just ane of the reasons why VirusTotal cannot be used for comparative testing. I volition exit it to VirusTotal to explain some more of the reasoning for this.
'BAD IDEA: VirusTotal for antivirus/URL scanner testing
'At VirusTotal we are tired of repeating that the service was not designed equally a tool to perform antivirus comparative analyses, merely as a tool that checks suspicious samples with several antivirus solutions and helps antivirus labs by forwarding them the malware they fail to detect. Those who use VirusTotal to perform antivirus comparative analyses should know that they are making many implicit errors in their methodology, the nigh obvious being:
'VirusTotal'southward antivirus engines are commandline versions, then depending on the product, they will non deport exactly the same as the desktop versions: for example, desktop solutions may utilise techniques based on behavioural analysis and count with personal firewalls that may decrease entry points and mitigate propagation, etc.
'In VirusTotal desktop-oriented solutions coexist with perimeter-oriented solutions; heuristics in this latter grouping may exist more aggressive and paranoid, since the bear upon of false positives is less visible in the perimeter. It is simply non fair to compare both groups.
'Some of the solutions included in VirusTotal are parametrized (in coherence with the developer visitor's desire) with a different heuristic/agressiveness level than the official end-user default configuration.
'These are just 3 examples illustrating why using VirusTotal for antivirus testing is a bad idea.' [8]
Virtually of the rest of the myths I describe are components of the comparative testing myth, but each is applicable to the common use of VirusTotal for purposes other than misguided product testing. These points are of import for the individual user to understand as well.
Myth two: Detection of malware on VirusTotal ways the scanner has detection of the malware
VirusTotal displays what a product says information technology detected. This does not mean that the scanner would detect that threat if it was on your computer. Equally VirusTotal explained, the vendors are free to configure their products as they wish to. It is non every bit simple as trying to configure your product the aforementioned way. A vendor can use undocumented switches to obtain heuristic detections that the user cannot. Although VirusTotal explains that heuristics may be unlike between perimeter solutions and desktop solutions, a command-line scanner can behave differently from either a desktop or perimeter solution. Vendors tin configure cloud detections in a manner that only detects scans from VirusTotal (or a exam lab).
In some cases a sample is detected past its wrapper alone. The actual threat within the wrapper may not exist detected. If the malware is present outside of its wrapper, so it may not exist detected.
Myth three: Lack of detection on VirusTotal means the file is rubber
Of course malware evading all virus scanners is extremely common. I do non demand to explain that to this audience. (This audience needs to explain that to their not-technical friends and family.)
I am referring to a state of affairs in which the presence of a clean file is indicative of the presence of harmful files. Although the file itself is harmless, the presence of the file is likely to signal the user is in a dangerous situation. I volition draw a file in this category subsequently in this paper.
Myth 4: Lack of detection on VirusTotal ways the scanner doesn't observe it
In some cases a vendor withholds displaying detection of a threat. At times it may be advantageous to have detection in the production on your desktop, simply not to brandish detection on virus-scanning services that malware authors may use to determine if their application is existence detected. In other cases detection of the threat is irrelevant due to other technologies that forbid infection without naming a threat.
Myth 5: Fake positive ways false positive
The same factors that brand VirusTotal unsuitable for comparative testing may affect the proper interpretation of false positives too. Frequently, stronger heuristics mean there will be more false positives. In the workspace a simulated positive can toll an enterprise a lot more than than a missed detection. On a consumer machine faux positives increment vendor support costs and decreases user satisfaction with their product. VirusTotal can serve a vendor well equally a testbed for new heuristics prior to public release of the new technology. A vendor one time explained to me that they would sometimes examination new heuristics on their free consumer products before adding them to their enterprise offerings. VirusTotal can assist to replace human being republic of guinea pigs.
Myth 6: More is amend
Researchers and the media akin volition frequently study that there is proficient, bad, or fair coverage of a threat submitted to VirusTotal. There is a difference betwixt detection and protection. Detection of a threat by 45 out of 60 scanners does not hateful that more people are protected from the threat than 1 which is detected by x out of threescore scanners. The reasons for this are marketplace share (past number of users) and, less frequently, geography. If five out of 55 product find a threat, and they are the v with the largest market place share, then more users will exist protected confronting the threat than if 30 scanners with minimal market share detect a threat and any of the top five scanners miss it.
According to the OPSWAT April 2017 market place share report, the 10 Windows virus scanners with the almost users account for 84.25% of the market share. (OPSWAT's demographics cannot be extrapolated to the enterprise market share. Due to the sample fix OPSWAT uses there will be significant differences in worldwide metrics.) The top four scanners were used by fifty.83% of the user base of operations. As long as the 5 scanners holding the majority of the market place share detect a threat, so all of the remainder of that set of scanners can miss the same threat and the majority of users will however be protected. The scanners with the largest marketplace share may exist significantly different in different geographical locations, for example China. If the summit Chinese scanners miss a mutual threat in Mainland china, the top scanners in the rest of the world are likely to be relatively inconsequential. When a piece of malware is rarely seen exterior of a specific country, as has previously been the case with some malware seen in Japan, the market place share of the top scanners in that country may be the but meaningful measure of global protection metrics.
In the following examples would the detection ratios be considered skillful coverage? Bad coverage? Fair coverage?
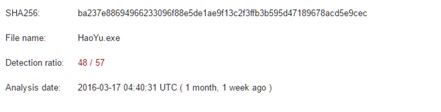 Figure 3: HaoYu.exe was detected by 48 of 57 scanners.
Figure 3: HaoYu.exe was detected by 48 of 57 scanners.
In Figure 3, nosotros see that HaoYu.exe was detected by 48 of 57 scanners, just look at who appears to take been missing detection at that time.
 Effigy 4: Symantec was missing detection of HaoYu.exe.
Effigy 4: Symantec was missing detection of HaoYu.exe.
If Symantec had detected the file and 30 scanners that did find the file had missed it, more than people may accept still been protected than what would appear to be the case in this example.
At this point it becomes essential to emphasize another difference between detection and protection. Security suites, such as that which Symantec offers, may not detect the file on VirusTotal, withal their users may withal be protected from the threat by other components of the production. This applies to many products, so even the number of protected users cannot be determined solely by the marketplace share and number of products detecting a threat on VirusTotal.
Four out of 57 scanners brandish detection for the sample shown in Figure five. Is that bad detection?
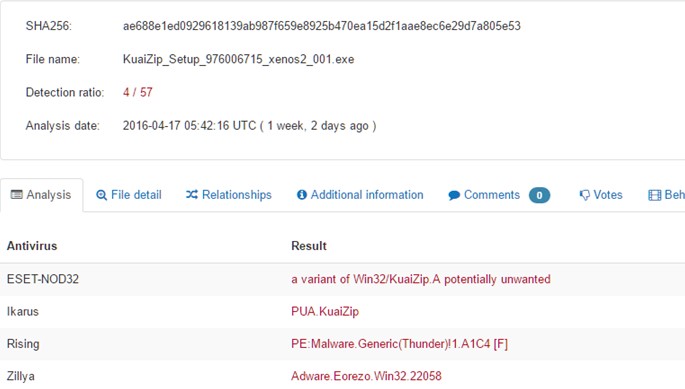 Effigy 5: 4 out of 57 scanners display detection.
Effigy 5: 4 out of 57 scanners display detection.
Based on iii out of the 4 products referring to the file as adware, one would exist inclined to say it is irrelevant, however a year later this sample was detected by 18 products. The composition of the detection types still favours adware or riskware, simply a exam lab could potentially defend the inclusion of this file in a comparative test set. The file communicates with IP addresses known to have hosted actual malware. In a testing situation where dynamic execution resulted in the download and execution of malware, the sample can reasonably chosen malware. Obtaining the application from the developer'southward website can be tricky since some AV products and browsers block the site itself. While there are times that a designation of adware, etc. is based upon legalities, vendor reputation, or fifty-fifty a chance analysis of the prevalent use of the file for chivalrous purposes, in some cases the take chances to consumers is such that a failure to provide any detection is undeniably harmful. Based upon the market place share of the scanners detecting this specific file, coverage on VirusTotal is poor at all-time.
How is the coverage on the post-obit file?
 Figure 6: File not found.
Figure 6: File not found.
Looking at VirusTotal lonely that mean solar day at that place was no fashion to decide if the file was clean, or even if the file was detected by all of the scanners. In the case of this specific file, coverage on VirusTotal was almost certainly abysmal. NSS Labs Baitnet discovered this file on half-dozen June 2017. OPSWAT's Metadefender had seen the file on four June and just three of 39 scanners detected the threat at the time of this scan on v June (Effigy vii). On 9 June VirusTotal indicates that 34 out of 61 products detected the file.
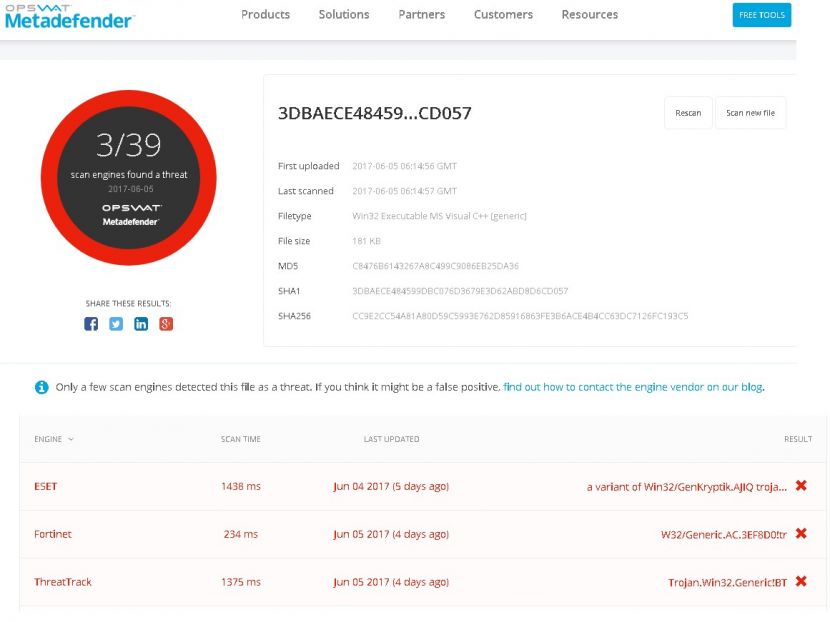 Figure 7: Simply 3 of 39 scanners detected the threat at the time of this scan on 5 June.
Figure 7: Simply 3 of 39 scanners detected the threat at the time of this scan on 5 June.
Based on the relationship to an exploit, OPSWAT'due south detection data and timing, also as information indicative of when most scanners on VirusTotal reported detection, it is reasonable to believe that prior to 9 June very few anti-virus scanners were able to detect the threat.
Myth vii: Malicious website ways malicious website
Legitimate websites are frequently compromised and may contain exploits, host phishing pages, or host malware. Maryhill Manor (Figure viii) is one such instance.
 Figure viii: Maryhill Estate.
Figure viii: Maryhill Estate.
The scan results of http://www.maryhillmanor.org (Figure 9) show the site is detected every bit malicious or suspicious past some products. At various times I have seen anywhere from one to 6 products reporting the site as dangerous. Maryhill Manor is a legitimate health care facility with a legitimate website. The problem is that the site has been compromised on several occasions.
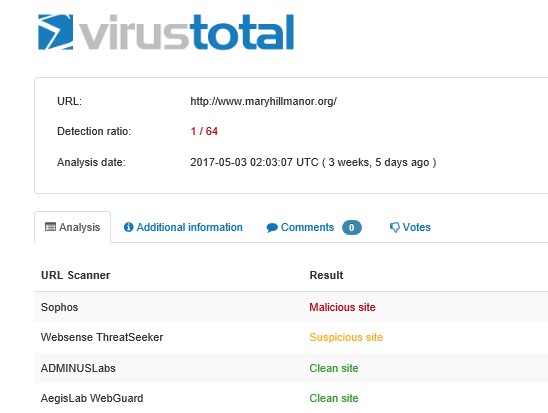 Figure 9: The Maryhill Manor site is detected as malicious or suspicious by some products.
Figure 9: The Maryhill Manor site is detected as malicious or suspicious by some products.
The scan shown in Figure 10 was a month or and then later on the previous browse (Figure 9) and the results are a little worse.
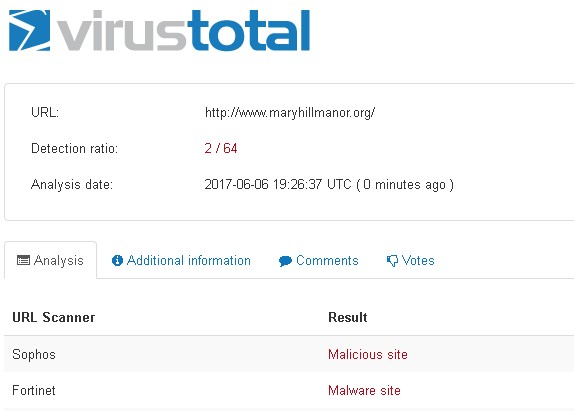 Figure 10: A browse of the Maryhill Manor site a month or so later.
Figure 10: A browse of the Maryhill Manor site a month or so later.
Once a site has been identified as hosting exploits, malware or phishing attacks, it can take a long time for scanners to remove detection. As is the example with near scans, VirusTotal does provide more contextual data well-nigh URL scans.
Beyond the scan reports
Once the results of a scan are returned in that location are tabs containing data that can heighten i'due south agreement of the nature of the threats. Not all tabs will exist provided for every submission. Make new submissions would be expected to take less contextual information bachelor.
Typically, there is less forensic data returned from URL scans than file scans, notwithstanding on the 'Additional Information' tab the IP accost resolution and scanning engine details tin be found.
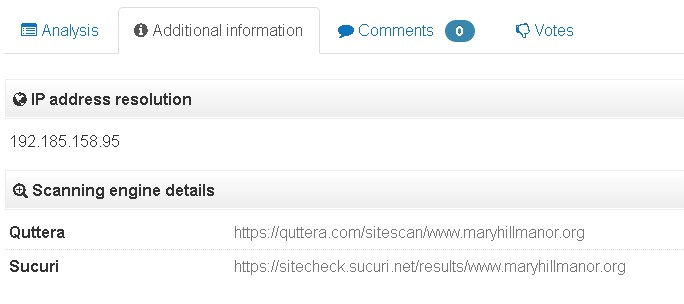 Figure 11: The IP address resolution and scanning engine details can be plant under the 'Additional Information' tab.
Figure 11: The IP address resolution and scanning engine details can be plant under the 'Additional Information' tab.
The scanners listed nether 'Scanning engine details' provide hyperlinks that volition initiate a new browse and return information such equally geolocation information or whether the site is blacklisted, etc.
Typically, there will exist far more data bachelor from a file scan than from a URL scan. This information can exist of assistance in agreement the technical details of the sample and in adding context to information technology.
Earlier in this paper I mentioned that fifty-fifty if a file is safe, its presence may bespeak an unsafe situation. In the following example I will use information provided by VirusTotal to accost the myths that state 'Lack of detection means the file is safety' and 'False positive ways faux positive'. I accept provided the URL for the example being discussed for readers who may wish to try some of the techniques used:
https://www.virustotal.com/en/file/43239bce0a3200c5d61d968f8e130dbaa3bf987e02417d49191c72bbf1636d4e/analysis/
This specific version of ravmond.exe, is a component of an older version of a legitimate Chinese anti-virus product.
Bkav is a large security company in Vietnam. Bkav was the merely scanner to report the file as adware or anything at all (Figure 12). Is this a example of a fake positive? Let'south dig a bit deeper. Nosotros will start with the 'File Detail' tab, shown in Effigy 13.
 Effigy 12: Bkav was the simply scanner to written report ravmond.exe as adware or anything at all.
Effigy 12: Bkav was the simply scanner to written report ravmond.exe as adware or anything at all.
 Figure 13: File details.
Figure 13: File details.
Farther down on the 'File Detail' page (non pictured) in that location is data nearly attributes of the PE file, as well equally debug data.
The file is digitally signed and timestamped, although information technology appears to be for a 2012 anti-virus product. Other research I take done supports the conclusion that the document is in club. This is i contextual component of our analysis that tends to support a determination of a false positive detection. In that location is not enough evidence to depict a conclusion at this time.
Carbon Black provides some interesting information on the 'Relationships' tab. Details include the hashes of files that wrote this sample to deejay, hashes of the files that the sample wrote to disk, files that were running at the time the samples were written to disk, the overlay parents. Hashes provided are hyperlinked, however some of the related files have not been submitted to VirusTotal. VirusTotal also reports on compressed bundles that the sample was included in.
Carbon Black reported it had seen eight files that wrote this sample to disk. A couple of the files were not present on VirusTotal and one to 13 scanners displayed detections for each of the other samples.
This sample of ravmond.exe wrote 50 files to disk. These files appear to exist clean and part of the Rising Antivirus production. At that place is withal nothing that indicates that this sample is malicious.
There is something interesting when y'all get downwards to the execution parents, as shown in Figure 14.
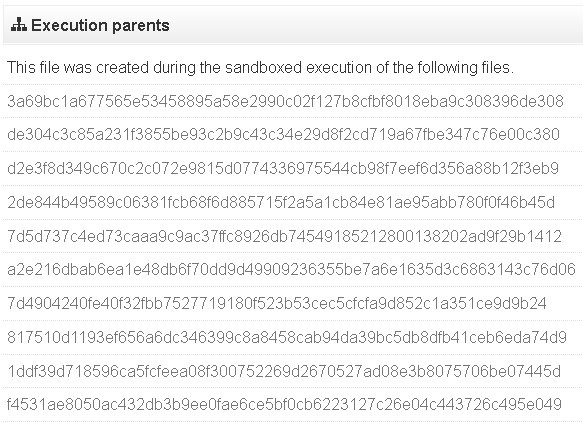 Figure fourteen: Execution parents.
Figure fourteen: Execution parents.
The hashes shown in Effigy xiv are from only a few of the execution parents. At that place were 50 files in all that Carbon Black reported as execution parents. Many, if not all of these files were detected by multiple scanners as adware, PUPs, or malware. One of the execution parents was especially interesting in that information technology was detected by AVG as 'Beijing Ascension Information Technology Corporation Express'. The file was digitally signed, notwithstanding the digital signature did not verify (MD5: 4ee6cfd6ca6c2e172095f2ca016d9e02). It is rare to identify malware by the proper name of a large security vendor, just I have encountered this detection proper noun on a dissimilar sample with a verified signature. Another execution parent was detected by VBA32 as Signed-Adware.Hao123.BaiduBeijingCo (MD5: fc234b76a106b8fd1f1abc30e43270d0f72da1ab).
There is a tab containing additional information virtually files, such equally file identification hashes, file size and type, etc. There is a listing of different filenames the ravmond.exe sample being discussed has been has been seen with, but those may have been renamed by researchers prior to being uploaded. For instance, 'vt-upload-Zdl8aB' is not likely to be a proper noun that the file was seen as in the wild. Nether behaviour characterization, Zemana reports dll-injection.
This file was dropped by an exploit and was one of several files dropped at the same time. The file was evidently part of a bundled software bundle that independent malware. Bkav was the merely 1 out of 61 scanners to detect the sample. From the information provided past VirusTotal via Carbon Black, this file is oft bundled with malware. The presence of the file on a computer that is non running a Chinese version of Windows is quite probable to indicate the presence of malware on the system. Ascent Antivirus volition not install on anything but a Chinese version of Windows. If a virus scanner detects the presence of this file on a calculator that is not using the Chinese version of Windows, it is reasonable to detect the file. If the file is found on a computer in China, and was not installed from the Beijing Rising website, information technology may be surrounded my malware as well. If the file is legitimately present, Beijing Rising is unlikely to detect information technology as malware, but may suggest the user install a newer version of the product. It is entirely possible for Bkav to omit detection from computers running a Chinese version of Windows. The safe file itself is an indication of danger on most computers. Just because this file is not detected information technology doesn't mean it is any safer than a good slice of cheese in a mousetrap is for a rodent. Detection of the file may be an unintentional false positive by Bkav, but this detection tin exist quite useful.
Voting and commentary
VirusTotal allows for voting on the rubber of a file, as well equally commenting on a file. As a rule, the voting is of no value. Empty zip files, operating system files, and many other plain clean files volition often accept votes indicating the files are malicious.
Comments will sometimes provide other third-party analysis and may be of value in those situations, even so comments like 'it's a bad file' are often related to false positives, and of grade add no value.
A few closing remarks
File and URL scanning are components of multiple security products. The NSS Labs Cyber Advanced Warning Arrangement (CAWS), ReversingLabs TitaniumCore and OPSWAT Metadefender are just iii examples of products that provide threat-scanning services, but only as a portion of more comprehensive security offerings. VirusTotal does non perform threat modelling or continuous incidence response, or data sanitization. If you believe a company offer threat submission and scanning services is similar VirusTotal, look again at the consummate offerings of that company earlier yous attempt to make a determination. As VirusTotal has explained, it does not supervene upon other security solutions.
VirusTotal is loved by users of all skill levels and throughout the world. Despite frequently incorrect conclusions, users do protect themselves from the installation of adware which may lead to more serious arrangement compromise – and frequently, unsupported conclusions are correct anyhow.
VirusTotal is also an important function of the security ecosystem. The bilateral data sharing with the security industry helps make the Cyberspace safer for all of united states.
References
[1] https://world wide web.virustotal.com/en/documentation/email-submissions/.
[2] https://www.virustotal.com/en/documentation/browser-extensions/.
[3] https://www.virustotal.com/en/documentation/desktop-applications/.
[4] https://www.virustotal.com/en/documentation/mobile-applications/.
[5] https://www.virustotal.com/en/documentation/public-api/.
[6] https://www.virustotal.com/en/faq/#virustotal-api.
[seven] https://www.virustotal.com/en/documentation/private-api/.
[viii] https://www.virustotal.com/en/nearly/.
Source: https://www.virusbulletin.com/virusbulletin/2018/01/vb2017-paper-virustotal-tips-tricks-and-myths/
Post a Comment for "Can You Upload Copyrighted Stuff on Virustotal"